TL;DR: Quantum computers will eventually break Bitcoin's cryptography, starting with exposed wallet keys tied to roughly 6.9 million BTC (including Satoshi Nakamoto's 1.1 million). BIP-360 and BIP-361 propose voluntary and mandatory migration paths, but every scenario (burn, move, or theft) will impact the market years before a true quantum-capable attack arrives. This piece covers the technical realities, the hard trade-offs ahead, the likely market impact, and what you can do right now.
This is not FUD. It is grounded in real data, with concrete numbers and verifiable sources. The largest identifiable cluster on the Bitcoin blockchain sits in plain sight: roughly 1.1 million BTC, untouched for over fifteen years, with public keys permanently exposed on-chain. These coins are widely believed to belong to Satoshi Nakamoto, and the prevailing assumption has long been that they will never move.
However, Satoshi-related coins are not the only relevant exposure. A broader set of early-era and long-dormant wallets, including lost keys, abandoned mining outputs, and inactive addresses from Bitcoin's first years (2009-2012), may account for an additional 0.1M to 0.5M BTC depending on classification models. Combined, these coins represent around 8% of the total supply, a concentration that could inevitably influence market dynamics if any meaningful portion were to move.
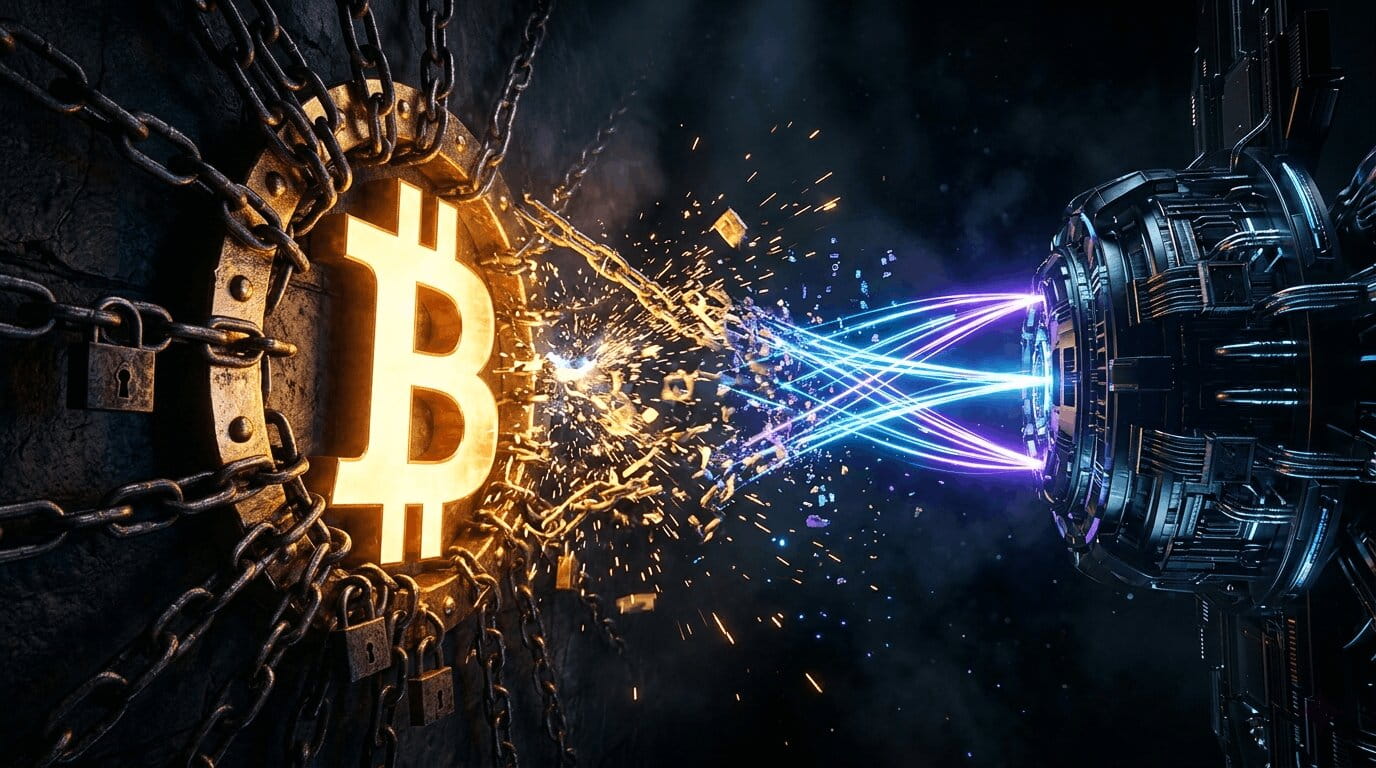
Quantum computing breaks that assumption. In modeled conditions approximately in nine minutes, a sufficiently powerful quantum computer could derive a Bitcoin private key from its public key. Google Quantum AI's March 2026 paper sharply lowered the resources needed to pull this off. No alarms, no early warnings, just wallets silently drained. The most exposed whale wallets are hit first like Satoshi's coins.
This is the part of the quantum conversation almost nobody is willing to address head-on. And it may be the most consequential part of all. The Bitcoin community will eventually be forced to choose between three outcomes for those coins, and every single one of them moves the market before quantum hardware ever arrives.
Burn. Move. Be Stolen. Three paths. Three futures for Bitcoin. None are quiet, they all move the market.
This article walks through the technical threat, the protocol response (BIP-360 and the more radical BIP-361), the migration tradeoffs, and most importantly, the Satoshi problem the rest of the industry keeps avoiding. By the end, you should understand not just whether quantum computers can break Bitcoin, but why the market will start pricing the answer long before Q-Day arrives.
How Does Bitcoin’s Cryptography Work?
The Two Pillars: ECDSA and SHA-256
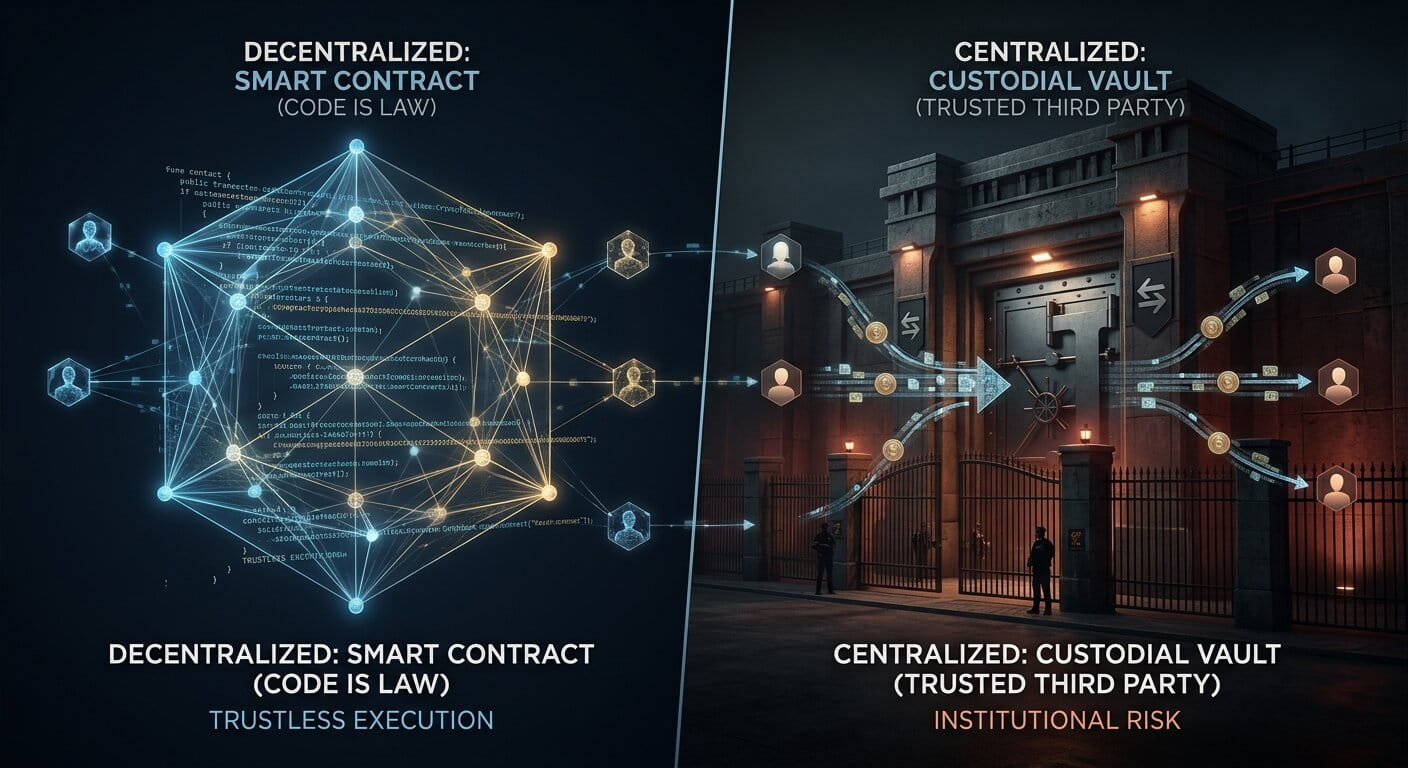
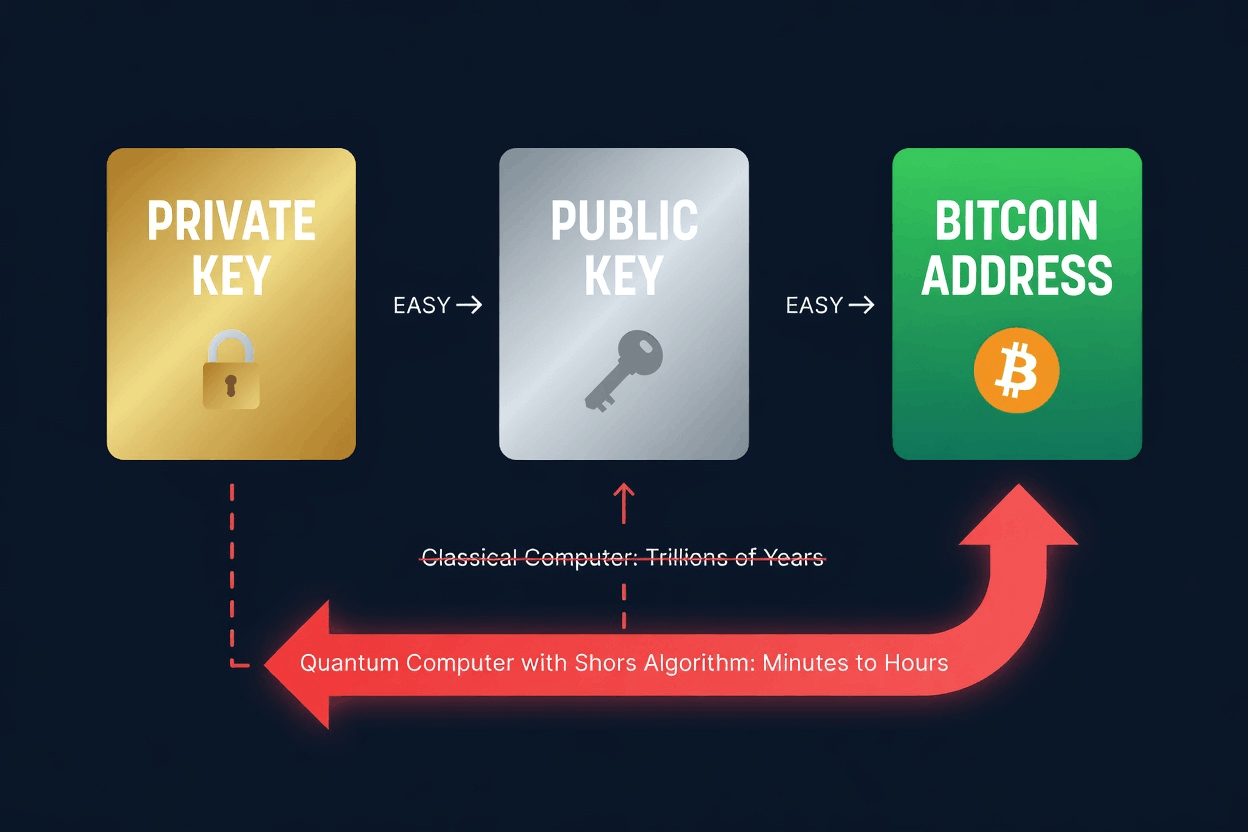
Bitcoin’s security rests on two systems. The first is ECDSA (Elliptic Curve Digital Signature Algorithm) on the secp256k1 curve. It links your private key to your public key with one-way math: easy to go forward, practically impossible to reverse on classical hardware. The second is SHA-256, the hash function used in mining and address generation. With modern address types like P2PKH or P2SH, your public key stays hidden behind a hash until you spend from that address.
If that one-way math ever becomes reversible, the entire signature foundation of Bitcoin is at risk. That is exactly what quantum computing threatens.
What About Mining? Does Quantum Threaten SHA-256?
Mining is largely resilient. Grover’s algorithm can accelerate brute-force search against SHA-256, reducing the effective security from 256-bit to roughly 128-bit, still far beyond any practical attack threshold. This does not break mining. It shifts it. A sufficiently advanced quantum miner would gain a competitive edge, potentially reshaping hash power distribution without compromising the integrity of SHA-256 itself.
The real target is not mining, but the system that determines control over coins.
Which Bitcoin Addresses Are Vulnerable to Quantum Computers?
Not every Bitcoin address carries the same level of risk. The key factor is simple: has the public key been exposed on the blockchain?
- Taproot addresses (starting with bc1p): The public key is visible by design. These are the most exposed modern address type.
- Pay-to-Public-Key (P2PK): The original format from Bitcoin’s earliest days. Public keys sit directly on-chain, fully visible. This includes all of Satoshi Nakamoto’s estimated 1.1 million BTC.
- Reused addresses: Any address you have already spent from has its public key permanently recorded on the blockchain.
- Unspent modern addresses (P2PKH/P2SH): If you have never spent from these, your public key is still hidden behind a hash. These are currently the safest type.
By various estimates, roughly 25–33% of all Bitcoin by value has its public key already exposed. According to Coinbase analyst David Duong, approximately 6.51 million BTC sits in quantum-vulnerable addresses, counting early P2PK outputs and reused addresses.
How Close Are Quantum Computers to Breaking Bitcoin?
What Can Shor’s Algorithm Actually Do?
The specific danger comes from Shor’s algorithm. In simple terms, it is a mathematical technique designed for quantum computers that can solve the exact type of math problem ECDSA relies on. If you give it a public key and enough computing power, it can figure out the corresponding private key.
Research from Roetteler et al. (2017) established the baseline: breaking Bitcoin’s 256-bit secp256k1 curve would require approximately 2,330 logical qubits and around 126 billion quantum logic gates (Toffoli gates). More recent work has tightened this range considerably. A September 2025 preprint analysis derived an algorithmic lower bound of just 523 logical qubits for secp256k1, placing the realistic vulnerability range at 523–2,500 logical qubits depending on assumptions about error correction and algorithm efficiency.
Then came the most consequential update yet. In 30 March 2026, Google Quantum AI, in collaboration with the Ethereum Foundation and Stanford University, published "Securing Elliptic Curve Cryptocurrencies against Quantum Vulnerabilities," which sharply lowered these estimates again. Using an optimized quantum circuit layout for elliptic-curve arithmetic and improved Toffoli gate decomposition, the researchers showed that breaking secp256k1 may require only 1,200–1,450 logical qubits, and fewer than 500,000 physical qubits under low-error superconducting architectures. That is roughly a 20× improvement over prior estimates, and the gain comes from better algorithms, not bigger machines. Google itself responded to its own findings by accelerating its internal post-quantum migration target to 2029.
How Fast Could a Quantum Computer Crack a Key?
Once a machine with enough stable qubits exists, the actual cracking happens disturbingly fast:
- At a 66.6 MHz clock frequency: roughly 6.5 days to crack an ECDSA key.
- At a 10 GHz clock frequency with lower error rates: roughly 30 minutes.
- Under the most optimistic hardware projections: as little as 10 minutes, fast enough to steal funds before a single Bitcoin block confirms.
Google’s 30 March 2026 paper added a more specific scenario: a “primed” quantum attack. The bulk of Shor’s algorithm can be pre-computed in advance, with no specific public key as input. Once a victim’s transaction hits the mempool and exposes its public key, the machine only needs to finish the final ~9 minutes of work to derive the private key. With Bitcoin’s 10-minute average block time, that gives an attacker roughly a 41% probability of stealing the funds before the original transaction confirms (Figure 6 of the paper). This is the “on-spend” attack, and it sits on top of the much larger problem of approximately 6.9 million BTC already sitting in addresses with permanently exposed public keys.
There would be no warning. If this capability appears, wallets with visible public keys could be emptied before anyone understands what is happening.
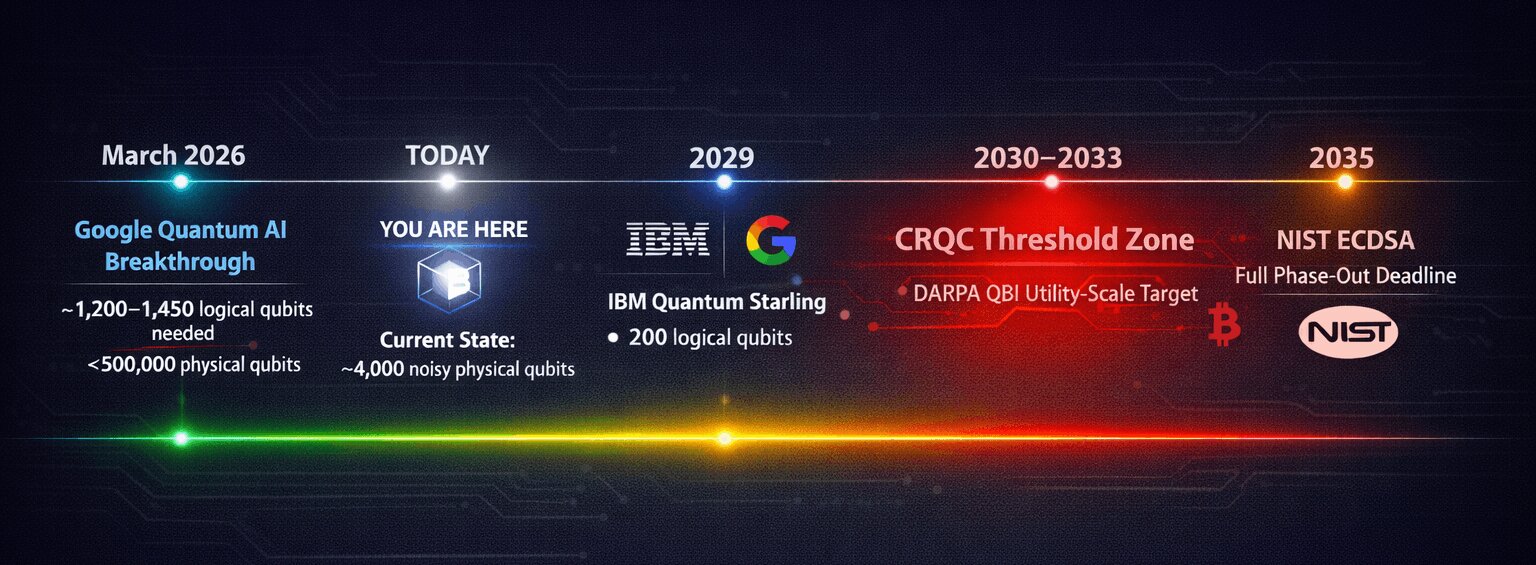
Where Does Quantum Hardware Stand Today?
As of early 2026, no quantum computer can threaten Bitcoin. The most advanced systems run a few thousand noisy physical qubits. Earlier estimates suggested that cracking Bitcoin's encryption would need roughly 1.9 billion stable ones after error correction. Google's March 2026 paper sharply revised that downward to fewer than 500,000, still roughly 500× beyond today's largest machines, but no longer a problem for future generations to solve.
But hardware roadmaps from the biggest players are converging on an aggressive trajectory:
- IBM projects 200 logical qubits by 2029 with its Quantum Starling system, capable of executing 100 million quantum gates, with a fault-tolerant quantum computer in the early 2030s. (IBM Quantum Roadmap)
- Google’s CEO Sundar Pichai has compared the current quantum moment to where AI was in the 2010s, estimating practical quantum computing is 5–10 years away. (Davos 2025 Interview)
- Microsoft’s Satya Nadella has stated their Majorana 1 chip could deliver a meaningful quantum computer “not in decades, but in years.” (Microsoft Ignite 2025)
- DARPA’s Quantum Benchmarking Initiative (launched 2024) is specifically investigating whether a utility-scale quantum computer could be built by 2033. Eleven companies have already advanced to Stage B evaluation.
- Respondents in a recent survey of global quantum experts indicated a 50% or greater probability that machines capable of breaking Bitcoin's cryptography will emerge between 2030 and 2035 Chaincode (Chaincode Labs, Bitcoin and Quantum Computing).
EXPERT INSIGHT
“Breaking cryptography is one of the easier applications for quantum computing. You can go to quantum-resistant codes in banking. Bitcoin is a little bit different, which is why people should be thinking about this right now.”
John M. Martinis, Nobel laureate in Physics and former head of Google’s quantum hardware group, endorsing Google Quantum AI’s March 2026 paper, via CoinDesk (April 2026)
The US, UK, EU, and China have all independently arrived at similar timelines: establish standards by 2026–2028, migrate high-priority systems by 2030–2031, and fully phase out elliptic curve cryptography by 2035. When multiple major governments reach the same conclusion separately, that signal deserves attention. (NIST IR 8547)
What Is the “Harvest Now, Decrypt Later” Problem?
There is another layer that makes this more urgent than it looks. The Bitcoin blockchain is public. Every exposed public key is already available for anyone to download and store today. State-level actors and well-funded organizations can collect these public keys right now and simply wait until quantum hardware catches up.
This is not speculation. Intelligence agencies have been documented stockpiling encrypted data for future decryption. With Bitcoin, the harvesting is already done by default: the blockchain sits on every full node worldwide. As CISA has warned, organizations must begin migrating to post-quantum cryptography now, not after quantum hardware matures.
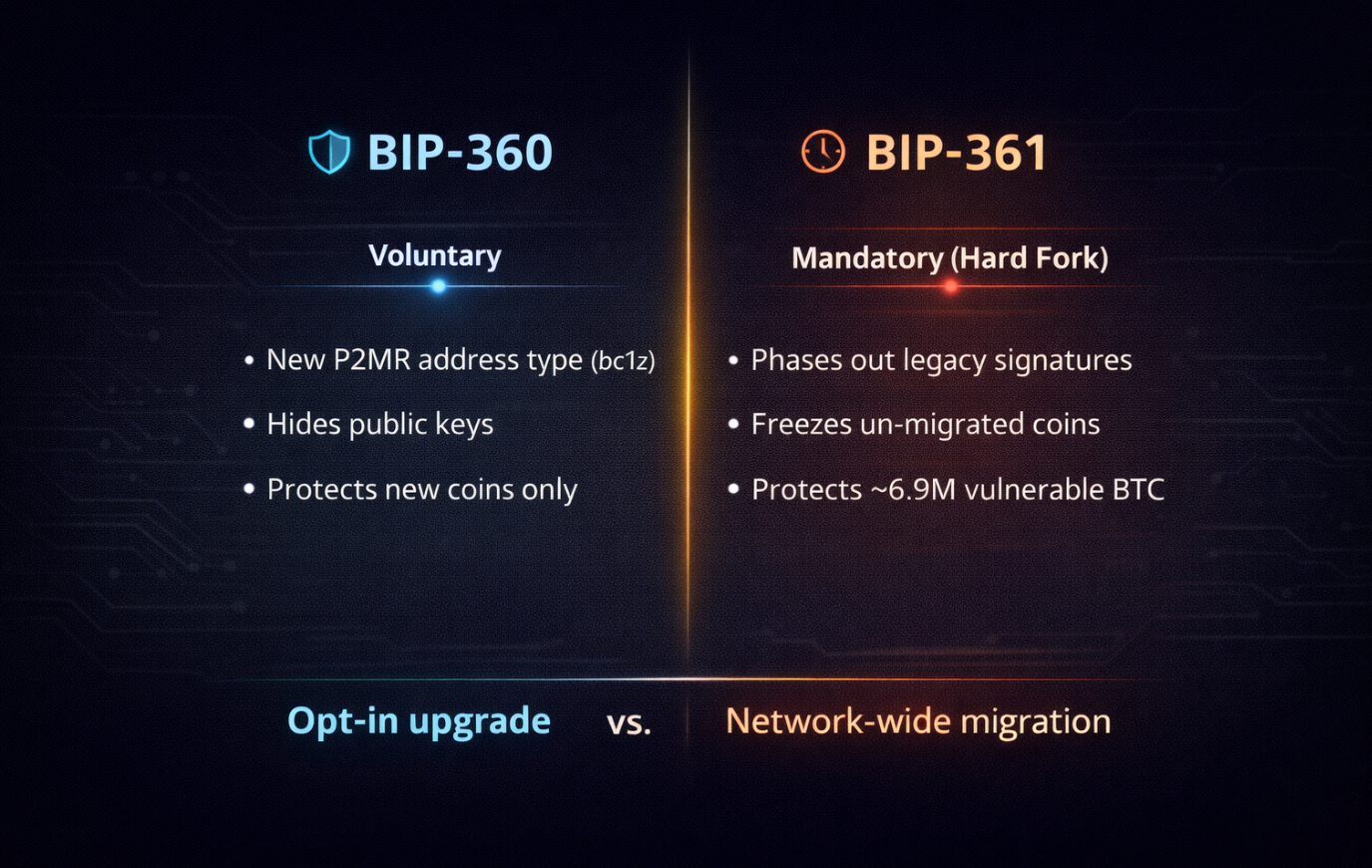
What Are BIP-360 and BIP-361? Two Paths to Quantum Resistance
BIP-360 was co-authored by Hunter Beast (senior protocol engineer at MARA), cryptographic researcher Ethan Heilman, and technical communications specialist Isabel Foxen Duke. It was merged into the official BIP repository on February 11, 2026. It introduces a new Bitcoin output type called Pay-to-Merkle-Root (P2MR).
How Does P2MR Work?
Current Taproot addresses include a key-path spending method that puts the public key directly on the blockchain. P2MR removes this entirely. Instead, it commits only to the Merkle root of a Tapscript tree, with no internal public key is exposed at all. When someone spends from a P2MR output, they reveal a script path and a proof of inclusion, but never a raw public key.
Because hash functions are far more resistant to quantum attacks than elliptic curve math, this approach dramatically shrinks the attack surface. P2MR addresses would start with “bc1z” under the current proposal.
|
EXPERT INSIGHT "BIP 360 is step one. It proposes a quantum-resistant output type that has the upgradability and features of P2TR without the quantum vulnerability." Ethan Heilman, BIP-360 co-author, via Cointelegraph Magazine (February 2026) |
BIP-360 Limitations: Why It Won't Stop Mempool Front-Running
BIP-360 is a first step, not a complete fix. Its authors have been clear about that. It protects against long-exposure attacks, where public keys remain on-chain for extended periods. However, as noted in the previous section, in its current form it does not protect against mempool front-running.
This leaves short-exposure attacks unaddressed, where a quantum attacker could intercept a transaction in the brief window between broadcast and confirmation.
Defending against short-exposure attacks requires a second, larger step: adding post-quantum signature algorithms directly into Bitcoin’s scripting system. Candidate algorithms include ML-DSA (Dilithium) and SLH-DSA (SPHINCS+), both standardized by NIST in August 2024. These are lattice-based and hash-based cryptographic systems respectively, designed specifically to resist both classical and quantum attacks.
Merging BIP-360 into the repository does not mean it has been endorsed, activated, or scheduled. It means it entered the formal discussion process. As of March 19, 2026, BTQ Technologies launched Bitcoin Quantum testnet v0.3.0 with the first working BIP-360 implementation: full P2MR consensus using SegWit v2, bc1z address encoding, five Dilithium post-quantum signature opcodes, and end-to-end wallet tooling. The testnet has attracted over 50 miners and processed more than 100,000 blocks. But Bitcoin Core itself has seen zero implementation progress, and mainnet activation remains years away.
BIP-361: The Mandatory Migration Proposal
BIP-360 is a critical first step, but it only protects newly created coins. It does not address the roughly 6.9 million BTC already sitting in quantum-vulnerable addresses, including Satoshi’s estimated 1.1 million BTC. To close that gap, Jameson Lopp and five co-authors introduced BIP-361 (Post-Quantum Migration and Legacy Signature Sunset) on April 15, 2026. Where BIP-360 offers a voluntary upgrade path, BIP-361 proposes a mandatory migration timeline with enforcement mechanisms.
BIP-361 lays out a three-phase schedule. Phase A (roughly three years after activation) would ban new deposits to legacy ECDSA and Schnorr addresses. Phase B (roughly five years after activation) would invalidate all legacy signatures entirely, effectively freezing any Bitcoin that has not migrated to quantum-safe addresses. Phase C would introduce a recovery mechanism using zero-knowledge proofs, allowing legitimate owners to prove possession of their BIP-39 seed phrase and reclaim frozen funds without exposing private keys.
The proposal is deeply controversial. It challenges Bitcoin’s foundational principle that “your keys, your coins” means permanent and unconditional ownership. It would freeze billions of dollars in dormant wallets, including Satoshi’s coins. And it requires a hard fork to implement. Supporters argue it is the only way to protect the entire network, not just users who voluntarily upgrade. Critics see it as an unprecedented violation of property rights within the Bitcoin protocol.
Can Bitcoin Migrate to Post-Quantum Cryptography Safely?
There is no clean path. Every option carries real costs, and the community will eventually have to choose which tradeoffs it can live with.
|
Can old wallets be protected without moving coins? No. Quantum resistance cannot be retrofitted onto existing address types. Every vulnerable wallet will eventually have to move its coins to a new address. The only question is whether that happens voluntarily, under market pressure, or by a protocol-enforced deadline. |
Option 1: Voluntary Migration (Soft Fork)
Add quantum-safe address types like BIP-360’s P2MR through a soft fork, and let users move coins at their own pace. It respects Bitcoin’s decentralized ethos but leaves billions in exposed coins unprotected and creates a two-tier market between safe and vulnerable coins. History suggests it would also be slow: SegWit took over 2.5 years to reach 50% adoption. This is why proposals like BIP-361 have emerged, pushing the community toward mandatory timelines before Q-Day arrives.
Option 2: Replace ECDSA With Post-Quantum Signatures
Swap ECDSA and Schnorr for quantum-resistant schemes like ML-DSA (Dilithium) or SPHINCS+. This is the full long-term fix, and also the most disruptive option. Post-quantum signatures dwarf today’s 64-byte ECDSA. The UTXO set would balloon from around 5 GB to roughly 296 GB under ML-DSA-65. Throughput could fall to about 1 transaction per second, and half to four-fifths of existing full nodes could be priced out by the new hardware demands.
Researchers are trying to soften this. On Delving Bitcoin, STARK aggregation (NIWA) aims to compress all post-quantum signatures in a block into a single proof. SHRINCS brings signature size down to 324 bytes. Neither has reached BIP stage yet.
Signature Algorithm Comparison
|
Metric |
ECDSA |
ML-DSA (Dilithium) |
SPHINCS+ |
|
Signature Size |
64 bytes |
~2,420 bytes |
~7,856 bytes |
|
Public Key Size |
33 bytes |
~1,952 bytes |
~32 bytes |
|
Quantum Resistant? |
No |
Yes (lattice) |
Yes (hash) |
|
NIST Standard |
2013 |
FIPS 204 (2024) |
FIPS 205 (2024) |
|
Throughput |
3–10 TPS |
~1 TPS |
Below 1 TPS |
Source: NIST FIPS 204 and FIPS 205, August 2024.
Option 3: Forced Migration With a Deadline (BIP-361)
BIP-361, and older proposals like QRAMP, lay out an enforced migration window. Under BIP-361, any coins not moved by Phase B are not burned but frozen: legacy signatures become invalid, and the coins stay unspendable until the owner proves seed possession through a Phase C zero-knowledge proof. This is the only approach that covers the entire network, including coins held by people who are inactive or unreachable.
The political cost is high. It requires a hard fork, the most divisive upgrade type in Bitcoin’s history. Coins in lost wallets, dead holders’ estates, or forgotten addresses (estimated at 3 to 4 million BTC) would be frozen. Phase C recovery softens this, but the underlying principle, “your keys, your coins,” still takes a hit. The Bitcoin Cash split in 2017 showed how ugly these fights can get, and this one would be bigger.
|
⚠️ If Q-Day Arrives Early Exchanges would likely halt withdrawals to vulnerable addresses. The mempool would flood with competing transactions, pushing fees out of reach for smaller holders. Custodians and Lightning nodes would scramble to rebuild around new signature formats. Anyone still in an exposed address would be racing a capable attacker. |
Is Phase C Actually Workable? Two Prototypes Say Yes
Phase C is the biggest question hanging over BIP-361. If the recovery proof does not work in practice, freezing coins becomes effectively permanent confiscation. Two working implementations shipped within 48 hours of each other in April 2026.
Roasbeef’s zk-STARK prototype (April 8, 2026). Lightning Labs CTO Olaoluwa Osuntokun released a working proof that lets a Taproot wallet owner prove their address came from a specific BIP-39 seed, without revealing the seed or private key. It generates proofs in under a minute on consumer hardware with a proof size around 2 MB (Bitcoinist).
StarkWare’s Quantum Safe Bitcoin (April 9, 2026). A hash-based scheme that works with Bitcoin Script as it exists today, no fork required. The catch is cost: roughly $75 to $200 per transaction, so it is positioned as a last-resort tool for high-value cold storage rather than daily use (CryptoTimes).
Why STARKs and not SNARKs: the zk-SNARK systems in wide use today (Groth16, PlonK, Halo2) rely on elliptic curves, which Shor’s algorithm breaks. zk-STARKs rely only on hash functions, so they stay secure under quantum attack. That is why Phase C proposals have converged on STARKs.
Last and the Most Reasonable Option: The Hybrid Path
In practice, the realistic path combines all four approaches. A soft fork first introduces quantum-safe addresses (Option 1). Post-quantum signature algorithms follow as the long-term destination (Option 2), once aggregation research brings the overhead down. An enforced deadline protects coins that never voluntarily migrate (Option 3), and zk-STARK recovery makes that deadline survivable for honest holders who miss it.
BIP-361 already formalizes this shape: Phase A introduces P2MR and bans new deposits to legacy addresses, Phase B invalidates legacy signatures, and Phase C offers zero-knowledge recovery for anyone who still holds their seed.
What is left to settle is the timeline, the exact parameters, and whether the community can accept that keeping “your keys, your coins” meaningful now requires an active upgrade.
What Happens to Satoshi’s Coins in a Quantum Scenario?

This is the part of the quantum conversation that almost nobody addresses head-on. And it may be the most consequential part of all. Satoshi Nakamoto's estimated 1.1 million BTC, worth roughly $80 billion as of April 14, 2026, sits in early P2PK addresses with public keys permanently exposed on-chain. Together with other Satoshi-era dormant wallets, these coins represent the single largest known quantum target.
|
EXPERT INSIGHT "There are proposals to freeze Satoshi’s coins and all pay-to-public-key addresses. These discussions entail more controversial and complex questions, as achieving consensus on such matters is exceedingly difficult." Isabel Foxen Duke, BIP-360 co-author, at ETH Denver (March 2026) |
Is Satoshi Really Dead? Why the Bitcoin Market's Biggest Assumption Is Being Tested
The dominant view in the Bitcoin community is that Satoshi is either dead, permanently unreachable, or deliberately silent. These coins have not moved in over 15 years. Many treat this as a feature: the idea that Bitcoin’s creator cannot manipulate the supply is part of what gives Bitcoin its perceived integrity.
That assumption is increasingly under public pressure. In October 2024, HBO’s Money Electric: The Bitcoin Mystery (directed by Cullen Hoback) put Bitcoin’s identity question back in the mainstream by drawing heavily on interviews with Blockstream CEO Adam Back before ultimately naming Bitcoin Core developer Peter Todd, who immediately denied it.
Then on April 8, 2026, the New York Times published an 18-month investigation by two-time Pulitzer winner John Carreyrou naming Adam Back as the strongest Satoshi candidate yet.
The case rests on AI-driven stylometric analysis of 134,308 cypherpunk and cryptography mailing list posts, Back’s authorship of Hashcash (cited in the Bitcoin whitepaper), the timing of Back’s silence during Satoshi’s active period, and a tense in-person confrontation in El Salvador. Back has repeatedly denied the claims, calling the evidence coincidence and confirmation bias.
There is still no cryptographic proof. Only signing a message with Satoshi’s keys or moving the coins would settle it. But for the first time, a credible mainstream investigation is asserting that Satoshi may be a specific, living, active CEO, which directly stresses the assumption that the 1.1 million BTC will simply sit forever.
My own reading: Adam Back is one of the very few early cypherpunks who has stayed in the trenches through every dark period Bitcoin has faced. From Hashcash in 1997 to founding Blockstream in 2014, pulling much of the Bitcoin Core development team under one roof, the man has never stopped building. He is still in the daily technical trenches, writing actively to nearly a million followers on X.
That kind of sustained commitment, combined with his visible discomfort in the HBO documentary and the weight of Carreyrou's 18-month investigation, makes him, in my view, a remarkably credible Satoshi candidate. This is a personal reading, not proof, and it carries no certainty. But the accumulation of circumstantial evidence is getting harder to dismiss.
Whether Back is Satoshi or not, a mandatory quantum migration deadline forces this assumption into the open.
If Satoshi Is Gone: The Burn Scenario
A burn deadline would permanently destroy 1.1 million BTC, roughly 5.2% of Bitcoin’s total supply. This would be the largest single supply reduction in Bitcoin’s history. Some argue this is economically positive for remaining holders. Others see it as an irreversible, community-imposed destruction of the founder’s stake.
If Satoshi Is Alive and Moves the Coins
If BIP-361 or a similar mandatory migration proposal is adopted, a hard deadline would force whoever holds those keys to act, and the market learns that Satoshi is alive and active. The immediate questions would be impossible to contain: Will they sell? Will they try to influence governance? Does Bitcoin have a living founder sitting on 5% of the total supply? The psychological shockwave could dwarf any quantum computing threat. BIP-361’s proposed timeline transforms this abstract thought experiment into a concrete ultimatum with a specific countdown.
The NYT’s April 2026 investigation makes this scenario less hypothetical: if Carreyrou is right that Satoshi is a living, identifiable person, then a forced quantum migration deadline is no longer a moral abstraction. It is a public ultimatum directed at a known individual.
If a Quantum Attacker Gets There First
If the community delays too long and a quantum-capable adversary derives Satoshi’s private keys, they take control of 1.1 million BTC. The fallout would go far beyond one theft. It would prove that Bitcoin’s underlying cryptography was broken. Trust in every other cryptocurrency relying on ECDSA would collapse along with it.
There is no scenario involving Satoshi’s coins that does not carry massive consequences.

Why The Market Will Price This Before Q-Day Arrives
Most quantum analyses stop at the technical question: when will a sufficiently powerful machine exist? But that misses the more important market question: when will Bitcoin’s price actually start reflecting the answer?
The honest answer is much earlier than most people think. And the reason has nothing to do with hardware timelines. It has to do with asymmetric information. Here are the likely scenarios and what could happen next, based on my reading.
If Satoshi Is Gone for Good (or Chooses not to Move the Coins)
Whoever holds those keys, if anyone still does, knows whether the coins will ever move. The community does not. As a quantum migration deadline draws closer, a credible burn starts to look unavoidable: 1.1 million BTC permanently destroyed, roughly 5.2 percent of total supply removed in a single event, the largest deflationary event in Bitcoin's history. Smart money and insiders do not wait for the deadline to price that in. Front-running begins the moment the burn becomes a realistic outcome, which is years before any actual hardware threat lands. $BTC could easily reach millions of dollars per coin years before Q-Day migration happens.
If Satoshi is alive and intends to sell. This is the uglier and less likely scenario. Someone who knows they will be forced to move 1.1 million BTC in a few years has every reason to start distributing earlier, quietly, through OTC desks and exchange relationships, alongside whatever insiders may share that knowledge. They would not wait for the deadline. They would use every micro rally and every macro bull run between now and then as exit liquidity, beginning with other positions well before the 1.1 million BTC itself.
From the outside, this looks like normal market action. From the inside, it is a multi-year, controlled distribution by the largest single holder in Bitcoin’s history.
The asymmetry is the entire point. In both scenarios, the people with insider information, who actually know what will happen to Satoshi’s coins, have years of head start over the rest of the market. Whether the coins burn or move, the price impact gets distributed across a long pre-event window, not concentrated on a single day. Anyone modeling Bitcoin’s next cycle without accounting for this is missing one of the largest variables on the board.
There is a third version of this story that nobody wants to consider out loud. Satoshi might not even be a single decision anymore. If the New York Times investigation is right and Satoshi is a living person operating a public company, then the question of what happens to those coins is no longer purely cryptographic. It becomes a legal question, a tax question, a corporate governance question, and a deeply personal one. The keys may not even sit under one roof.
Whatever the outcome, this will go down as one of the defining events in Bitcoin’s history. A quantum migration deadline would not just be a technical upgrade. It would be the moment Bitcoin’s longest-running mystery is forced into the open, and the moment the market finally has to price the answer.
How Long Would a Full Migration Take?
BIP-360 co-author Ethan Heilman has estimated that even under optimistic conditions, everyone agreeing on the plan immediately, Bitcoin would need roughly seven years to reach full quantum resistance:
- BIP finalization, code review, and testing: approximately 2.5 years.
- Activation and deployment: approximately 6 months.
- Wallet, exchange, custodian, and Lightning Network upgrades: 1–2 years.
- User migration (every holder moves funds to new addresses): 1–3 years, given Bitcoin’s 3–10 TPS throughput.
- Legacy coin resolution (the hardest decision unmigrated coins): unknown timeline, could take years of debate alone.
Total: 7 years minimum under ideal conditions. Based on how Bitcoin governance has actually worked historically (SegWit took roughly 8.5 years from concept to widespread adoption, Taproot about 7.5 years), researchers estimate 10–15 years is more realistic. Given the urgency, I expect the community to act swiftly and, hopefully, complete the full migration in less than four years.

The core problem is arithmetic. The threat window is estimated at 4–10 years. The migration window is estimated at 5–10 years. Those numbers do not leave room for the kind of slow, cautious consensus-building that Bitcoin is known for. A rushed emergency migration under active threat would be far more damaging than a carefully planned proactive one. Every month of delay narrows the margin further.
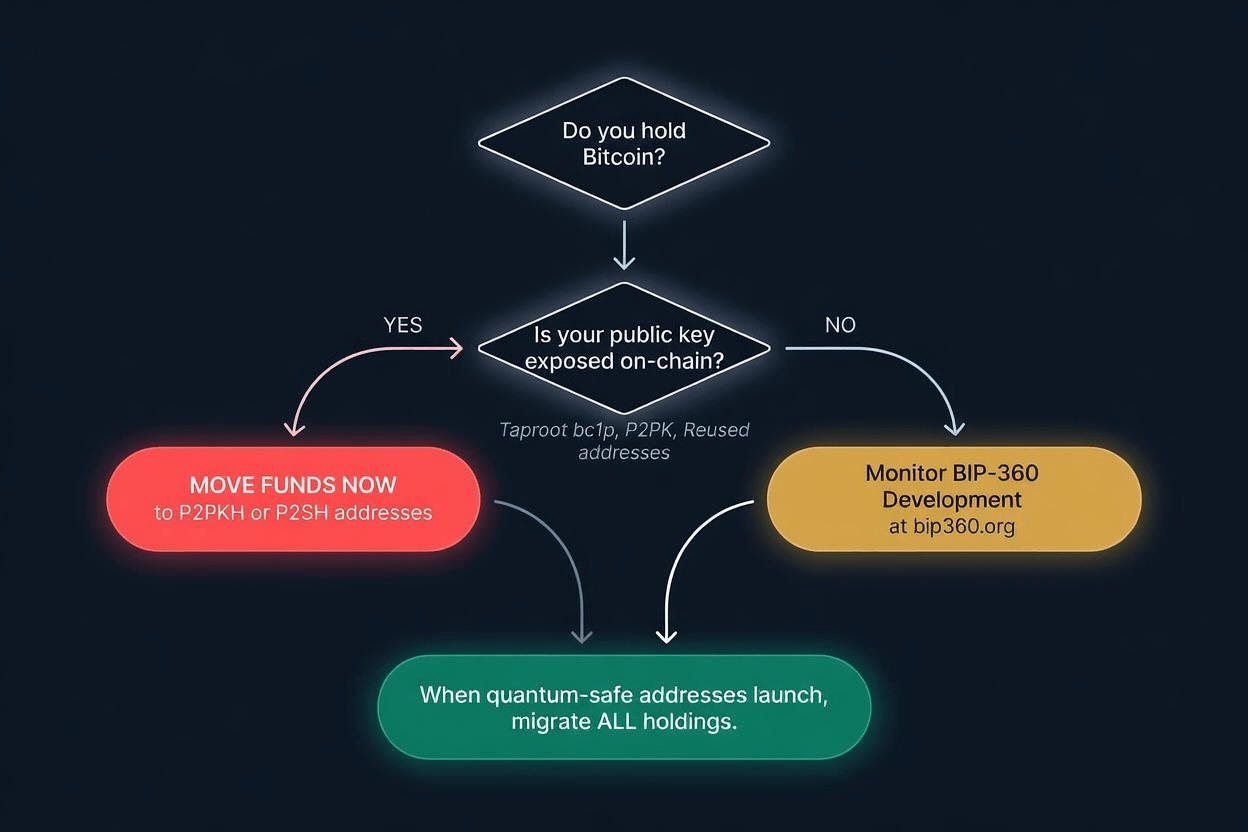
What Can and Should Bitcoin Holders Do Today?
While the protocol-level debate continues, individual holders can take concrete steps right now to reduce their own quantum exposure:
- Stop reusing addresses. Every time you spend from an address and then receive more funds at the same address, you expose your public key permanently. Use a new receiving address for every transaction.
- Move funds away from Taproot (bc1p) addresses if you are concerned about long-term quantum exposure. Unspent P2PKH and P2SH addresses keep your public key hidden until you spend.
- Use a wallet that generates new addresses automatically. Most modern wallets do this by default. Hardware options include Ledger, Trezor, and BitBox02. Popular software wallets include Sparrow, Electrum, and BlueWallet. Either way, it is worth double-checking your settings.
- Follow BIP-360 development. When quantum-safe address types become available, plan to migrate early rather than waiting for deadlines. Track progress at bip360.org.and bip361.org
- Avoid storing large amounts in any single address for extended periods. Spread holdings and rotate addresses periodically. This greatly narrows down the attack surface.
These steps do not make your coins quantum-proof. Nothing can do that until the protocol itself is upgraded. But they significantly reduce the risk that your specific coins would be targeted first.
Conclusion: The Decision Bitcoin Community Cannot Avoid
Encryption is always easier than decryption. This is a solvable problem. For all the pressure quantum computing puts on Bitcoin, the underlying story is still one of human response: can the community move faster than the math? I believe Bitcoin will adapt and come back stronger, as it has through every previous challenge. But that outcome is not automatic. Dismissing the quantum threat as a decade away, as some prominent figures still do, is not a strategy. It is a bet with other people's money.
The signs of serious preparation are finally appearing. Coinbase established a Quantum Advisory Board in January 2026 featuring Scott Aaronson and Dan Boneh, and on April 2, 2026, CEO Brian Armstrong publicly pledged personal oversight of Bitcoin's quantum resistance effort, launching an industry coalition with Bitcoin Core developers. The Ethereum Foundation formed its own post-quantum security team. Google moved its internal migration deadline up to 2029. Awareness is accelerating, and that is a good thing.
Nobody seriously debates whether quantum computers can break Bitcoin anymore. They will. What remains unclear is whether Bitcoin's notoriously slow governance process can outrun the hardware timelines, and whether smart money is already quietly positioning for the outcome.
The gap between BIP-360 and BIP-361 captures the fork in the road ahead. BIP-360 offers a voluntary, gradual path to quantum resistance for new coins. BIP-361 forces the question for all coins, including the oldest and most politically sensitive holdings on the network. The emergence of BIP-361 has shifted the debate from “do we need quantum resistance?” to something far harder: “is Bitcoin willing to break its own rules to save itself?” The answer to that question will determine not just the fate of Satoshi’s coins, but the soul of the protocol.
Because in the end, the quantum deadline is not just a cryptographic event. It is the moment Bitcoin's largest unanswered question, what happens to the 1.1 million coins held by someone who may or may not still be reachable, stops being a philosophical debate and becomes a forced decision. Whoever holds those keys, whoever knows the answer first, will be positioned years ahead of the rest of us.
Quantum hardware is on a schedule. Bitcoin's governance is not. The market will decide which one catches up first.
Frequently Asked Questions
Can quantum computers break Bitcoin today?
No. As of early 2026, no quantum computer has anywhere near the power required to threaten Bitcoin’s cryptography. Current machines have a few thousand noisy physical qubits. The most recent estimate, from Google Quantum AI’s March 2026 paper, puts the requirement at roughly 1,200–1,450 logical qubits, or fewer than 500,000 physical qubits under low-error superconducting architectures, a sharp downward revision from earlier figures (which ranged up to 1.9 billion physical qubits). The threat is real but not imminent. Most estimates place a capable machine in the 2030–2035 window.
What is Q-Day?
Q-Day is the hypothetical moment when a cryptographically relevant quantum computer (CRQC) becomes capable of breaking the cryptography that secures Bitcoin, Ethereum, and most of the internet. Most credible estimates place Q-Day in the 2030–2035 window, though Google’s March 2026 paper and follow-up research have compressed that timeline significantly. Q-Day is not a single event but a threshold: once crossed, previously safe cryptographic assumptions collapse.
Does quantum computing threaten Bitcoin mining?
No, not meaningfully. Bitcoin mining relies on SHA-256 hashing, which Grover’s algorithm could theoretically speed up but only by a quadratic factor, reducing effective security from 256 bits to 128 bits. 128 bits is still far beyond any practical attack. As BIP-360 co-author Hunter Beast put it at ETH Denver 2026, breaking 256-bit hash cryptography with Grover’s would require “a quantum computer bigger than the moon.” The real quantum threat to Bitcoin is signatures, not mining.
What is the on-spend attack?
An on-spend attack is a quantum threat scenario where an attacker intercepts a Bitcoin transaction in the mempool, derives the private key from the exposed public key during the time window between broadcast and confirmation, and broadcasts a competing transaction to steal the funds. Google’s March 2026 paper estimated that with a sufficiently advanced quantum computer and Bitcoin’s 10-minute average block time, this attack has a roughly 41% success probability per block interval.
Which Bitcoin addresses are most vulnerable to quantum attacks?
Addresses where the public key is already visible on the blockchain: Taproot (bc1p) addresses, early Pay-to-Public-Key (P2PK) addresses from Bitcoin’s first years, and any address that has been reused after spending. Addresses that have never been spent from (P2PKH, P2SH) keep the public key hidden behind a hash and are currently safer.
When could quantum computers realistically threaten Bitcoin?
Expert estimates vary. Industry roadmaps from IBM, Google, and Microsoft point to fault-tolerant quantum computers in the late 2020s to early 2030s. DARPA’s QBI program is evaluating whether utility-scale machines can be built by 2033. NIST plans to fully phase out ECDSA by 2035.
What is BIP-360?
BIP-360 is a Bitcoin Improvement Proposal that introduces a new address type called Pay-to-Merkle-Root (P2MR). It works similarly to Taproot but removes the key-path spending method that exposes public keys on-chain. It was merged into the official BIP repository in February 2026 as a first step toward quantum resistance, but has not been activated on the network.
What is BIP-361 and how is it different from BIP-360?
BIP-361 (Post-Quantum Migration and Legacy Signature Sunset) is a far more comprehensive and mandatory proposal introduced by Jameson Lopp and co-authors in April 2026. While BIP-360 introduces a new voluntary quantum-safe address type (P2MR) for new coins, BIP-361 targets all existing vulnerable coins by phasing out legacy ECDSA and Schnorr signatures on a strict timeline. It proposes three phases: banning new deposits to old address types (Phase A), invalidating all legacy signatures and freezing unmigrated coins (Phase B), and offering seed-based recovery via zero-knowledge proofs (Phase C). BIP-361 requires a hard fork and is deeply controversial because it would freeze dormant holdings, including Satoshi’s estimated 1.1 million BTC, if they are not moved before the deadline.
Can Bitcoin upgrade to quantum-safe cryptography without a hard fork?
Partially. New quantum-safe address types (like P2MR) can be introduced via a soft fork, letting users voluntarily migrate. However, fully protecting the network, including freezing or burning coins in old vulnerable addresses, would likely require a hard fork and community consensus on the treatment of unmigrated coins.
What happens to Satoshi’s coins?
Satoshi’s estimated 1.1 million BTC sit in P2PK addresses with permanently exposed public keys. In a mandatory migration scenario, these coins would either be burned (if Satoshi cannot move them), moved (revealing Satoshi is alive and active), or stolen by a quantum attacker if the community waits too long. There is no outcome that avoids significant consequences.
Will Satoshi’s coins move before Q-Day?
Probably not in the literal sense. But the price impact of those coins moving (or being burned) will likely be priced in by the market years before any actual quantum hardware exists. Anyone with credible knowledge of Satoshi’s intentions, or the keys themselves, has a strong incentive to distribute exposure quietly during normal market cycles rather than wait for a single deadline event. The asymmetric information advantage starts working long before the math does.
Will quantum computing crash Bitcoin’s price?
Not directly, and not on a single day. The bigger market risk is the slow, multi-year repricing as the community confronts what happens to vulnerable coins, especially Satoshi’s. A managed migration could be neutral or even bullish (if Satoshi’s coins burn, supply tightens by roughly 5 percent). A panic migration under active threat would be far more damaging. The outcome depends almost entirely on how early Bitcoin’s governance starts the process.
Are the bitcoins on my cold wallet (hardware wallet) safe from quantum attacks?
Mostly yes, but with a catch: safety depends on whether your public key has ever been exposed on-chain, not on whether the wallet is cold or hot. Hardware wallets like Ledger or Trezor protect your private key from malware, phishing, and remote theft, which is their job. But quantum computers do not attack private keys directly. They attack public keys. Once a public key has appeared on the blockchain, it stays there forever, and cold storage does nothing to hide data that is already public. The same rule applies to software wallets, paper backups, and metal seed plates: the storage medium is irrelevant, only the on-chain exposure matters.
The practical rule: if your address has never sent a transaction and uses a modern SegWit or Taproot format (bc1... or bc1p...), you are quantum-safe for now. If your address has ever spent funds, its public key is exposed, and you should plan to migrate those coins to a fresh, unused address well before a cryptographically relevant quantum computer arrives. Once BIP-360 or a successor activates, migrating again to a post-quantum address will be the final step.
How can I protect my Bitcoin from quantum computing right now?
Five concrete steps reduce your exposure today. First, never reuse addresses, since spending from an address permanently exposes its public key. Second, if you are still holding coins in addresses that have already broadcast transactions, move them to fresh, unused addresses, ideally modern SegWit (bc1q...) addresses where the public key stays hidden until the next spend. Third, split your holdings across multiple addresses instead of concentrating everything in one, so that a single exposed key never puts your entire stack at risk. Fourth, avoid storing large amounts in Taproot (bc1p) addresses, which expose public keys by design on key-path spends. Fifth, follow BIP-360 development and plan to migrate early when quantum-safe address types become available, rather than waiting for a deadline.
And stay alert to scams. Expect a wave of phishing emails, fake “firmware updates,” bogus “quantum-resistance upgrades,” and impostor support messages designed to exploit quantum panic and steal your keys or seed phrase. Always verify updates through your wallet provider’s official channels, never click links in unsolicited messages, and remember that no legitimate wallet will ever ask for your seed phrase.
None of these steps make your coins quantum-proof, but together they significantly reduce the chance that your specific coins are targeted, by quantum computers or by the scammers who will try to exploit the fear of them.
Which Blockchains Are Vulnerable to Quantum Computing?
The main quantum threat comes from Shor's algorithm, which can extract private keys from publicly exposed wallet keys (ECDSA and EdDSA). Mining algorithms like SHA-256 are far more resistant, quantum attacks only offer a minor speedup there, not a real break. But the actual risk level depends on how each chain exposes wallet keys. A network that hides public keys behind hashes is safer than one where every address is a visible public key. Here's how the major networks compare as of April 2026:
|
Network |
Signature |
Wallet Risk |
Notes / Status (April 2026) |
|
ECDSA (secp256k1) |
HIGH |
Total quantum-vulnerable ~6.9M BTC. BIP-360 (P2MR) and BIP-361 (mandatory migration) in progress. |
|
|
ECDSA (EOAs) |
HIGH |
Account-based: all EOA public keys exposed on first tx. Post Quantum team formed Jan 2026 |
|
|
Ed25519 |
HIGH |
Address = public key (always exposed). Winternitz Vault experiments ongoing. |
|
|
ECDSA (secp256k1) |
HIGH |
EVM blockchain, same exposure as Ethereum. No PQ roadmap. |
|
|
ECDSA (secp256k1) |
HIGH |
Same as Bitcoin. No independent PQ effort. |
|
|
ECDSA (secp256k1) |
HIGH |
Same as Bitcoin. No independent PQ effort. |
|
|
ECDSA (secp256k1) |
HIGH |
Merge-mined with Litecoin. Same exposure. |
|
|
ECDSA (secp256k1) |
HIGH |
Old Ethereum PoW clone. No PQ roadmap. |
|
|
ECDSA (secp256k1) |
HIGH |
Masternodes do not protect wallet signatures. |
|
|
ECDSA (secp256k1) |
HIGH |
PQ initiative announced by Justin Sun on 15 Apr 2026. All wallets still ECDSA. |
|
|
Ed25519 (EdDSA) |
MEDIUM |
UTXO model delays key exposure until spend. Lattice-based PQ research ongoing. |
|
|
ECDSA + Ed25519 |
MEDIUM |
~7.76M XRPL accounts have exposed. PQ testnet (Dilithium/ML-DSA) live since late 2025. |
|
|
Ed25519 (EdDSA) |
MEDIUM |
Stealth addresses + ring signatures reduce real-world key exposure. |
|
|
ECDSA + zk-SNARKs |
MEDIUM |
Shielded pool transactions hide public keys. Transparent pool remains exposed. |
Risk classification based on wallet-level public key exposure as of April 2026.
In short: No major chain is fully quantum-resistant yet. Industry-wide migration to post-quantum signatures (Dilithium, SPHINCS+) will be required. More importantly, every individual wallet must migrate funds to new quantum-resistant addresses to be protected. However, there are various projects, that produce quantum-resistant blockchain solutions are listed here in our quantum resistant coins category.
About the author:
Kripto Raptor is the Chief OG at OGAudit.com and an independent Web3 researcher, entrepreneur, and blockchain analyst. He has been active in the crypto space since 2016 and has worked full-time in the industry since 2020. His work focuses on analyzing Web3 projects through security, community behavior, and market dynamics. At OGAudit, he produces independent research, crypto audit content, and project evaluations.
Sources
[1] BIP-360: Pay-to-Merkle-Root (P2MR). Co-authored by Hunter Beast, Ethan Heilman, Isabel Foxen Duke. Merged February 2026. https://bip360.org/
[2] BIP-361: Post-Quantum Migration and Legacy Signature Sunset. Jameson Lopp et al. April 2026. https://www.bip361.org/
[3] IBM Quantum Roadmap: Path to Large-Scale Fault-Tolerant Quantum Computing by 2029. https://www.ibm.com/quantum/blog/large-scale-ftqc
[4] DARPA Quantum Benchmarking Initiative (QBI), Launched 2024. https://www.darpa.mil/research/programs/quantum-benchmarking-initiative
[5] Chaincode Labs. “Bitcoin and Quantum Computing: Current Status and Future Directions.” (Bitcoin Post-Quantum report). https://chaincode.com/bitcoin-post-quantum.pdf
[6] Carreyrou, J. “New York Times investigation naming Adam Back as Satoshi Nakamoto candidate” (April 8, 2026). https://www.nytimes.com/2026/04/08/business/bitcoin-satoshi-nakamoto-identity-adam-back.html
[7] Coinbase Independent Advisory Board on Quantum Computing and Blockchain (January 2026). https://www.coinbase.com/blog/coinbase-establishes-independent-advisory-board-on-quantum-computing-and-blockchain