🚨 Don't let your wallet be an open diary! Most crypto solutions are NOT private. Think you don’t need privacy-focused blockchains yet? Your opinion may change soon. We reviewed the Top 7 Privacy Blockchains of 2025. Monero is still king for payments, but new ZK networks like Zcash, Aleo, and Aztec are redefining private transactions and privacy in DeFi. Find out which one will actually protect you. This guide compares 7 leading solutions by real anonymity, decentralization, regulation risk and adoption.
When Bitcoin appeared in 2009, it arrived during a period when central banks and governments were expanding the money supply to stabilize financial markets. Many early users viewed this ability to create unlimited fiat currency as a source of long-term inflation and evidence that traditional systems could alter their rules whenever needed. Bitcoin introduced a different approach built on decentralization. It relied on a permissionless peer to peer network, a fixed supply and predictable issuance. Its transparent on-chain ledger allowed anyone to verify transactions, understand the system and operate without relying on banks or other intermediaries. Although it did not provide strong privacy, the combination of decentralization, open verification and a public ledger felt like a clear alternative. Bitcoin and later Ethereum functioned as open, immutable records, and that openness was viewed as a form of fairness rather than a drawback.
But like every powerful tool, it turned out to be a double-edged sword. That same transparency that lets you verify a transaction also lets attackers map your entire financial life. Today’s hackers don’t need your home address or your social security number. If they can link your wallet address to your real-world identity (you exposing them or via data breaches, KYC leaks, phone numbers, or social media activity), they can see your on-chain balance and then deploy targeted social engineering attacks to trick you into exposing your private keys or signing a malicious transaction.
But it’s not just the bad guys you have to worry about. That same transparency is becoming the ultimate tool for governments to track your every move, aiming to tax unrealized gains or roll out surveillance measures that crush basic human rights. As happened recently, when the UK government jeopardized the right to privacy of its citizens.
If you’re reading this, it’s probably because that thought already makes you uneasy. You don’t just want “crypto”.
So grab your coffee and get comfortable because I have made this comprehensive, up-to-date and unbiased report on the Best Privacy Blockchains in December 2025 (which will be valid for a long time probably in 2026 too!).

The Illusion of Self-Custody Safety: Why Your Crypto Wallet is Always a Target
Imagine this scenario: Julián, a successful crypto trader, sat back in one of Manhattan’s most expensive restaurants, finishing his steak and swirling his red wine.
“Yes, bro… Waiting for BTC to dip to $67K so I can buy the dip load more,” he said, loud enough for three tables to hear. Flexing.
The waiter, Elias, listened in silence. Nobody there knew that last month he read Russian cybersec forums about crypto hacks. He was looking for potential preys for days, and his waiter job was just a cover.😅 He had already seen Julián’s Instagram username by looking at the phone on the table and was about to execute his sneaky plan.
When the bill came, Elias staged a quick “connection error” with the card terminal. He leaned in, apologetic but smooth:
“Sir, the bank network is down. Since you clearly know crypto… maybe just shoot me the $300 in USDT? I’ll put the cash in the register myself and save you the wait.”
Julián, eager to show off, agreed. QR shown, transaction sent.
“Done, champ. Keep the change.”
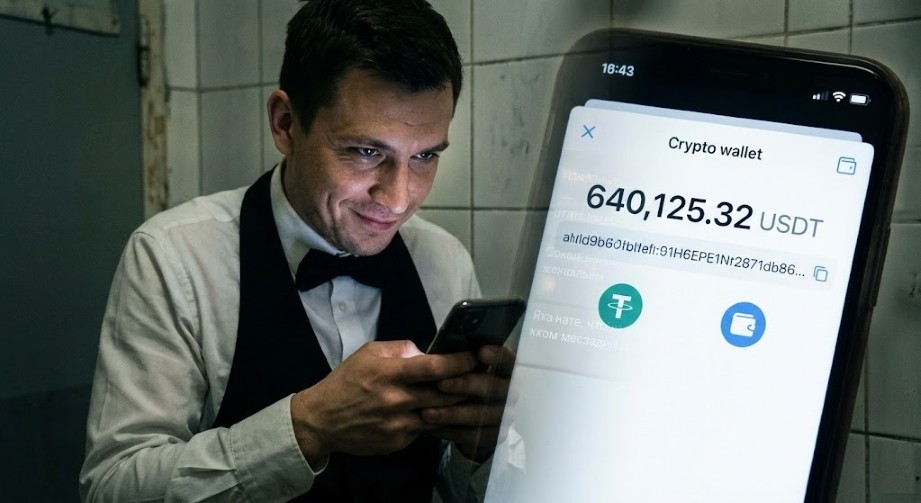
Five minutes later, in the staff bathroom, Elias opened the transaction hash on his phone. He went to the blockchain explorer and looked for the sender's (Julián's) address. It didn't took long before he discovered his wallet balance: 641,125USDT💰.
He smiled and typed into a secret Telegram chat:
“Target: Male, 30s. Arrogant. Wallet: Balance: ~$640k liquid. I have his instagram username. Waiting for attack vectors.”
The dinner was over, but the hunt had just begun. Because soon after, Julián's wallet and social accounts were all over the crypto hacker forums.
What “Privacy” Really Means on a Blockchain
What’s about to happen to Julián could happen to almost anyone who mixes money and ego. The only “crime” so far is that the waiter looked up a public crypto wallet address. That’s normal, even encouraged, in most blockchains: every transfer, balance and interaction sits on an open ledger, waiting for curious eyes, bots and attackers.
Blockchains were designed like glass banks: transparent, auditable, hard to fake. That’s brilliant for verifying payments or proving reserves, but terrible if someone links your real identity to that glass account. Once they do, phishing, SIM swaps, malware, wallet-drainer links, fake support chats and “friend” scams become sniper shots, not random noise.
That’s why more users now look for blockchains that feel less like glass and more like curtains. In practice, “privacy” usually means breaking the easy link between your everyday identity and your on-chain activity, even if that bends the original ideal of fully public, perfectly traceable, one-size-fits-all transparency.
What Are Privacy Coins and Privacy Blockchains?
If you’ve ever stared at your wallet balance and thought, “If someone else could see this, I’d be in trouble”, you’re already halfway to understand the real difference between private coins and private networks in 2025.
Because they exist for that exact tension: you want the benefits of crypto like fast payments, self-custody, no bank manager breathing down your neck asking why someone just sent you $10,000.
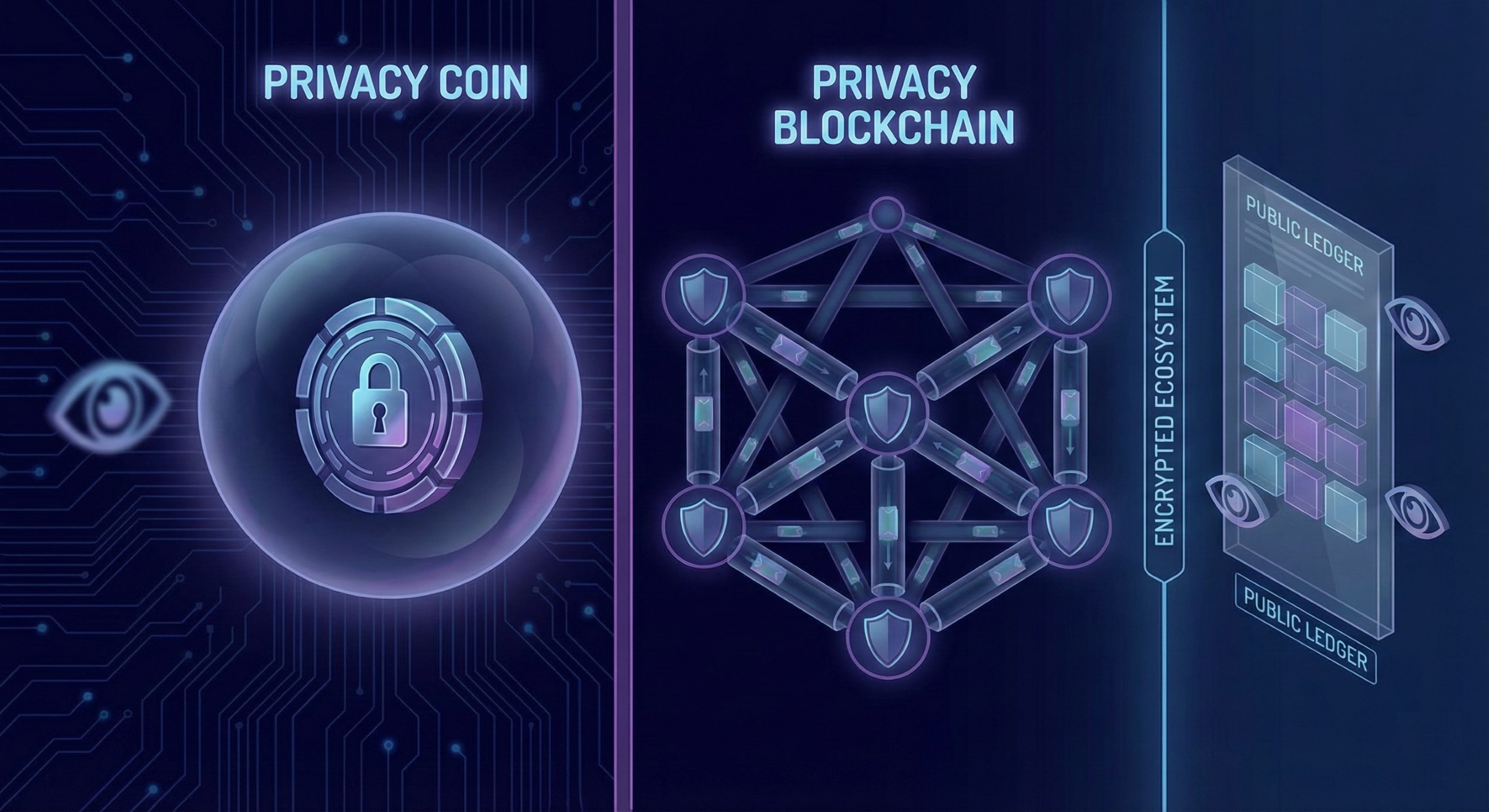
What are privacy coins?
They are specific cryptocurrencies designed with built-in anonymity features at the token level. Instead of sending “Alice → Bob → 2.5 coins” in plain view, they use tricks like ring signatures, stealth addresses or zero-knowledge proofs. These are cryptographic methods that hide who sent what to whom while still proving to the network that the transaction is valid.
Bring it back to the waiter story. If he had been paid by Julián in a true privacy coin like Monero instead of USDT on a transparent chain (Ethereum, Tron, BSC, etc.) , the waiter could still get paid, but he wouldn’t be able to click a block explorer and instantly see a neat “$641,125” balance sitting behind that wallet address.
(There are also strong ZK and privacy-focused network solutions that support decentralized stablecoins, which I will cover in another article in the coming months.)
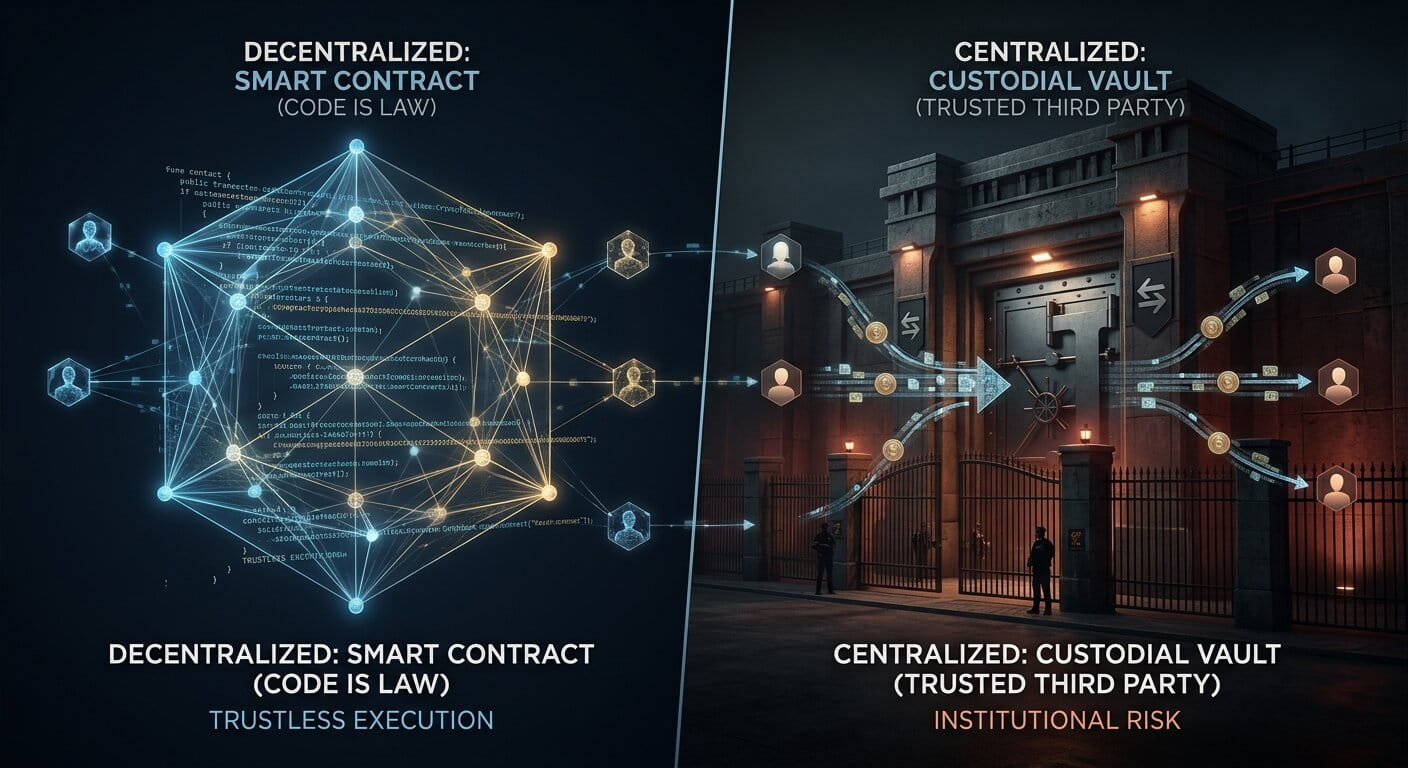
What are Privacy blockchains or privacy networks?
Pay close attention because they go a step wider: they aren’t just about one coin, they’re entire chains or ecosystems designed around private-by-default transactions or smart contracts.
Here, the focus is the infrastructure: the consensus, nodes, and execution layer are built so apps, DeFi (Fintech and DeFi Explained), NFTs (Non-Fungible Tokens) or messaging can run with obfuscated data, shielded states or encrypted transactions.
Now imagine a slightly smarter version of Julián using a privacy network. He still holds a stablecoin or a normal token, but he pays through a private L1 or L2 where the transaction is routed in an encrypted way.
Elias (the waiter) gets his $300 equivalent, the restaurant gets its cut, but anyone spying on-chain from home doesn’t clearly see: “this specific iPhone wallet, at this specific restaurant in Manhattan, has ~640k liquid.” In other words, privacy coins try to hide the money itself; privacy networks try to hide the entire environment where that money moves like location, timing, relationships, and patterns.
Top 7 Blockchain Privacy Solutions: Overview, Use Cases, and Editor’s Choice
Before jumping into names, it’s important to be clear: this is not just a list of “privacy coins to the moon”, it’s a review of networks, full ecosystems where apps, wallets and developers live. For this section I not only stayed in a lab reading whitepapers; I also went through real conversations on every place on the internet. Looked at real user reviews on CT (X Social), Reddit and OGAudit.
What follows is a carefully ranked summary an easy-to-read comparison of the 7 privacy-first blockchains that in 2025 are perceived as the strongest options for people who want to move, build or live on-chain with as little public exposure as possible.

Monero ($XMR): Battle-Tested Privacy Blockchain for Censorship-Resistant Payments
Monero would be like a boring and sensible adult at the crypto party. No flashy VCs, no airdrop drama, just a chain that’s been quietly letting people move money off-radar for almost a decade, using ring signatures, stealth addresses and confidential transactions by default.
- Which problem Monero solves? If you want to pay someone without your entire financial history being traceable forever, you should use Monero ($XMR) for everyday private payments, tips, payroll, gray-area commerce or donations under oppressive regimes. Even though it can be costly during peak busy times, one transaction costs often well below 10 cents. See average costs on Monero Blockchain Explorer by diving into the blocks/hashes
- What are the main risks of using Monero: Monero faces several technical privacy risks. Some non-standard nodes could attempt to collect network metadata, such as transaction timing or IP addresses, to deanonymize participants. Additionally, academic research continuously develops heuristics to analyze transaction patterns and trace activity. Constant exchange delistings could be a problem when cashing out in case you cannot find a good OTC dealer. Regulatory risks has now unfortunately materialized, not just for Monero but all privacy default blockchains: The EU's AML rules confirm $XMR will be delisted from regulated exchanges by 2027,(I'm afraid more countries may follow the EU path) regulators enforcing delistings is confirming its front-line vulnerability.
- Why do so many users still prefer Monero? Certainly people feel less like a product and more like a culture. It has the longest real-world track record of any serious privacy chain and genuinely grassroots governance, so there’s no company switch anyone can flip to turn it off. Another reason is high liquidity across multiple protocols and among Crypto OG OTCs makes it a strong choice. Without this liquidity and user base, cashing out or buying $XMR would be difficult and could result in significant slippage. Also some merchants accept $XMR both online and IRL.
That’s why many power users describe Monero as “old school but reliable”: when the question becomes “What do I trust to not leak my life if everything else fails?”, a lot of people quietly move their serious money to $XMR and just don’t talk about it too loudly.

Pirate Chain ($ARRR): Maximalist “Always-On” Privacy Blockchain for Fully Shielded Transactions
Pirate Chain is what you get when someone looks at Zcash and says: “Cool tech, now rip out the transparent mode and burn it.” It’s a niche chain, sure, but privacy purists love that there are no half-measures: you’re either fully shielded, or you’re not using it at all.
- Which problem does Pirate Chain ($ARRR) solve as a privacy coin?
It tackles the “optional privacy” issue: on chains where only some transactions are private (i.e. Zcash), those private ones stand out. Private Chain makes every normal transaction private by default.
- How does the Pirate Chain privacy model work for always-on anonymous payments?
It uses Zcash-style zk-SNARKs (see on Pirate Chain Whitepaper) with mandatory shielded addresses and transactions, so 100% of P2P activity is encrypted and there’s no transparent pool left for chain-analysis tools to fingerprint.
- What are the main risks and why do some users still choose Pirate Chain?
Liquidity is thin, the ecosystem is smaller and the pirate branding plus full-time privacy make it a big regulatory target.
Yet many “CT (Crypto Twitter) pirates” still prefer $ARRR when they want ghost-mode payments, happily routing it over Tor (Anonymous Internet Routing) and accepting that if they ever need deep DeFi or big liquidity, they’ll probably bridge out.

Aleo Network ($ALEO): Zero-Knowledge L1 for Fully Private dApps
Aleo is like the kid who shows up with a custom-built engine and starts redesigning the whole car. It takes the concept of privacy and expands it far beyond simple currency. While other chains focus on hiding "who sent what," Aleo is building a platform where the applications themselves run in total secrecy.
- Which problem Aleo solves? If you don’t just want private transfers but also private logic, Aleo steps in. Think private orderbooks, on-chain KYC without doxxing, payroll and business workflows that run on-chain without leaking internal data to competitors, employees or random chain-analysts.
- What are the main risks of Aleo Network? It has classic new-L1 risk: relatively concentrated early validator set, complex ZK tooling that’s still maturing, and the big adoption question of “will developers actually move here or stay in familiar EVM territory?”, which can slow ecosystem growth.
- Why do so many users and builders still bet on Aleo in 2025? Because it feels like a full-stack ZK design, not a patch. The whole VM, language (Leo Programmig Language) and infra are shaped around private computation, which attracts serious builders who need more than shielded transfers or one privacy precompile.
That’s why many devs describe Aleo as “still infrastructure phase, but with real upside”: when the question becomes “Where can I build a dApp that’s private by default, not as an afterthought?”, a lot of long-term builders quietly spin up on Aleo and accept they’re playing a multi-year game, not chasing next week’s pump.

Aztec Network: Private Ethereum L2 for Confidential DeFi and Hidden On-Chain Strategies
Aztec is what happens when Ethereum maxis finally admit they want privacy but refuse to leave the Ethereum universe. Instead of jumping to a new L1, they get a zk-rollup Layer-2 (See top Layer 2 Projects) with an architecture promising fully private smart contracts and encrypted DeFi while still inheriting mainnet security and liquidity.
- Which problem does Aztec Network solve for Ethereum DeFi users?
It tries to solve problems comes with fully transparent DeFi on Ethereum: every bid, liquidation, LP move and rebalance can be copied or front-run by maximal extractable value - MEV bots and copy-traders. Aztec introduces privacy layers to protect users’ actions from being exploited in this way.
- What are the main risks of using Aztec Network as a private Ethereum L2 in 2025?
It carries smart-contract and rollup complexity risk, depends on the L1 for finality, and raises fresh regulatory questions once you get fully private DeFi at scale. Let's talk about mixer-level opacity, but programmable and composable.
- Why do so many DeFi users still prefer Aztec Network for confidential DeFi?
Because you keep Ethereum’s liquidity, tooling and culture while adding end-to-end programmable privacy. For many funds and advanced traders, that’s far better than migrating to a brand-new L1. ETH DeFi folks call it “finally, a way to hide size and intent”, while skeptics worry it might become too private for regulators once serious volume arrives.
Bonus info: Aztec is currently conducting a public token sale for $AZTEC, open until December 6, 2025. So far, total bids have reached 15,374 ETH, approximately $46 million USD. More details can be found here: https://sale.aztec.network/ NFA: Not a financial advice! Please review tokenomics, token-use case vesting schedule carefully before aping in.
Oasis Network ($ROSE): Privacy-Enabled L1 with Confidential ParaTimes
Oasis is that chain everyone has vaguely heard of, but most people have never actually opened a wallet for. While CT (Crypto Twitter(now: X) Community) was busy yelling about the latest meme coin, Oasis quietly shipped privacy tech for data, things like credit scoring, health information or AI models, long before “zk everything” became the new buzzword.
- Which problem Oasis Network (ROSE) solves for real-world data privacy?
It targets projects that can’t just dump user data on a transparent chain without breaking laws or common sense: credit scoring, healthcare records, AI training data, user analytics and other Web2-style datasets that need both privacy and verifiable computation.
- What are the main risks of using Oasis as a privacy L1 in 2025?
Oasis relies heavily on hardware-based Trusted Execution Environments (TEEs), which adds a different trust surface. If that hardware layer is compromised, confidentiality can be too. On top of that, the validator set and ecosystem are smaller than Ethereum-based options, which can limit liquidity and mindshare.
- Why do builders still choose Oasis Network (ROSE) for privacy-first apps?
Because it fits a very specific niche: teams navigating GDPR (the European data protection law that regulates personal data) alongside AI and other data-protection rules, while still wanting blockchain guarantees. It’s less a “dark money coin” and more a “compliant data economy” solution, with confidential ParaTimes designed precisely for this combination of regulation and decentralization.
Midnight: Privacy-Focused Sidechain for Cardano ($ADA)
Midnight is a privacy-focused sidechain built for Cardano, introducing a “rational privacy” approach without risking delistings. It uses its own tokens, $NIGHT and $DUST (explained here), to enable private transactions and confidential smart contracts.
- Which problem Midnight solves?
Cardano users previously lacked a native way to handle sensitive data or shielded value without leaving the ecosystem. Midnight provides $ADA holders with a built-in privacy rail, allowing private activity while remaining secured by the broader Cardano network.
- What are the main risks of Midnight as a rational privacy solution?
It is still in its early stages as Documentation, tooling and UX are evolving positively. Also, the compliance-friendly design might cap how “absolute” the privacy can be in practice. Hardcore privacy maxis worry that features like selective disclosure could become pressure points for regulators later on.
- Why do so many users still get excited about Midnight in 2025?
Because it is a direct bridge. For many $ADA holders, that feels like finally having a serious privacy layer without abandoning their home chain, even if the trade-off is “regulated-friendly” rather than fully unplugged.

Zcash ($ZEC): Original zk-SNARK Privacy Chain Now Pivoting to “Encrypted Money”
If Monero is the quiet privacy veteran, Zcash is the scientist's grandparent who finally decided to dress a bit cooler. It started life as “Bitcoin with optional privacy”, spent years half-used and half-ignored, and now in 2025 is trying to relaunch itself as true “encrypted electronic cash” thanks to better wallets, Unified Addresses and more people actually using shielded pools.
- Which problem Zcash solves as a privacy coin in 2025?
Same root problem as Monero: Bitcoin’s total transparency. The Zcash privacy network wants fully encrypted payments plus the option to selectively reveal information with view keys when you need audits, taxes or compliance checks without doxxing everything.
- What are the main risks of Zcash as an encrypted money network?
For years, optional privacy weakened the anonymity set: many users bounced funds in and out of the shielded pool, leaving linkability traces. Add regulatory pressure and the “transparent pool legacy”, and Zcash still carries trust baggage that hardcore privacy maxis don’t easily forget.
- Why do some users still see Zcash as a revival play in 2025?
Because under the dust there’s serious cryptography, specifically Zero-Knowledge Proofs, and maturing infrastructure. If the “Zcash encrypted money” narrative sticks and most users truly adopt shielded-by-default wallets, Zcash ($ZEC) could solidify its place among the top 3 privacy coins. This outcome hinges on a substantial rise in active user count, not just a short-term price pump.
Check out recent deep dive article about Zcash, which covers its technical specifications, comparative analyses, and recent $ZEC price action.
And to track market data, learn more about other solutions, project links and read user reviews for these privacy solutions and more, visit our Privacy or Privacy Blockchain (Solutions) Category
How to Choose the Best Privacy Blockchain
If Julián really insists on flexing around with more than half a million in liquid crypto, his worst move was paying from the same transparent wallet that holds everything. For that scenario, a chain like Monero or Private Chain would have made much more sense for the actual payment, keeping his main stash in a separate setup entirely.
But technology alone will not protect him. Even on a strong privacy network, if he keeps talking loudly about his balance, reusing addresses, mixing personal phone numbers with wallets, and bragging on social media, he is still broadcasting attack vectors. These days, social engineering attacks are far more advanced than simple phishing links or fake support chats. Attackers routinely scrape public profiles, cross-reference usernames, track posting habits, monitor friend lists, and use leaked data from old breaches to build extremely accurate profiles. With enough fragments, they can impersonate contacts, reset accounts, bypass weak verification steps, and trick victims into revealing sensitive information without ever touching blockchain analytics.
I hope you now have a clear picture of the best privacy blockchains that really help you to stay safe and tranquil. Now you just need to choose the one (or two) that best fit your needs. Do your own research and compare them carefully.
As for my personal take, if I need absolute anonymity for payments, Monero is my undisputed choice because privacy is mandatory by default, leaving no room for user error. However, for using dApps and smart contracts, I lean towards Aztec or Midnight, as they allow me to protect my strategies without losing access to the liquidity of the broader ecosystem.
Avoid becoming someone like Julián who exposes sensitive information publicly. Even if you share your social accounts, never discuss your wallets, trades, or portfolio size if you do not fully understand the risks and know what you are doing. Strong privacy tools are useful, but they cannot compensate for careless habits such as oversharing, address reuse, or weak personal discipline. Learn from Julián’s mistakes and protect your financial activity with consistent, intentional privacy practices.
Thank you for reading my work. If you have any questions or suggestions about the topic, feel free to get in touch. You can also DM me on X (Twitter) (CryptoOGApe)
Disclaimer: This content is for educational purposes only and does not constitute financial or investment advice. Cryptocurrencies are volatile assets; always conduct your own research (DYOR) before making decisions. OGAudit is not responsible for any losses incurred.